How we’re protecting your Postman API keys in GitHub
With more than 10 million people worldwide using Postman, we take security very seriously and are committed to protecting our community from vulnerabilities.
Here’s the most recent example of that commitment:
Developers contribute code to open source projects in GitHub every day; unfortunately, during this process sometimes security credentials are shared by accident. So Postman has implemented a new token-scanning service in GitHub. This service will send you a notification if you accidentally commit a Postman API key to a public repository on GitHub, giving you a chance to respond quickly before there’s any unauthorized access to your data.
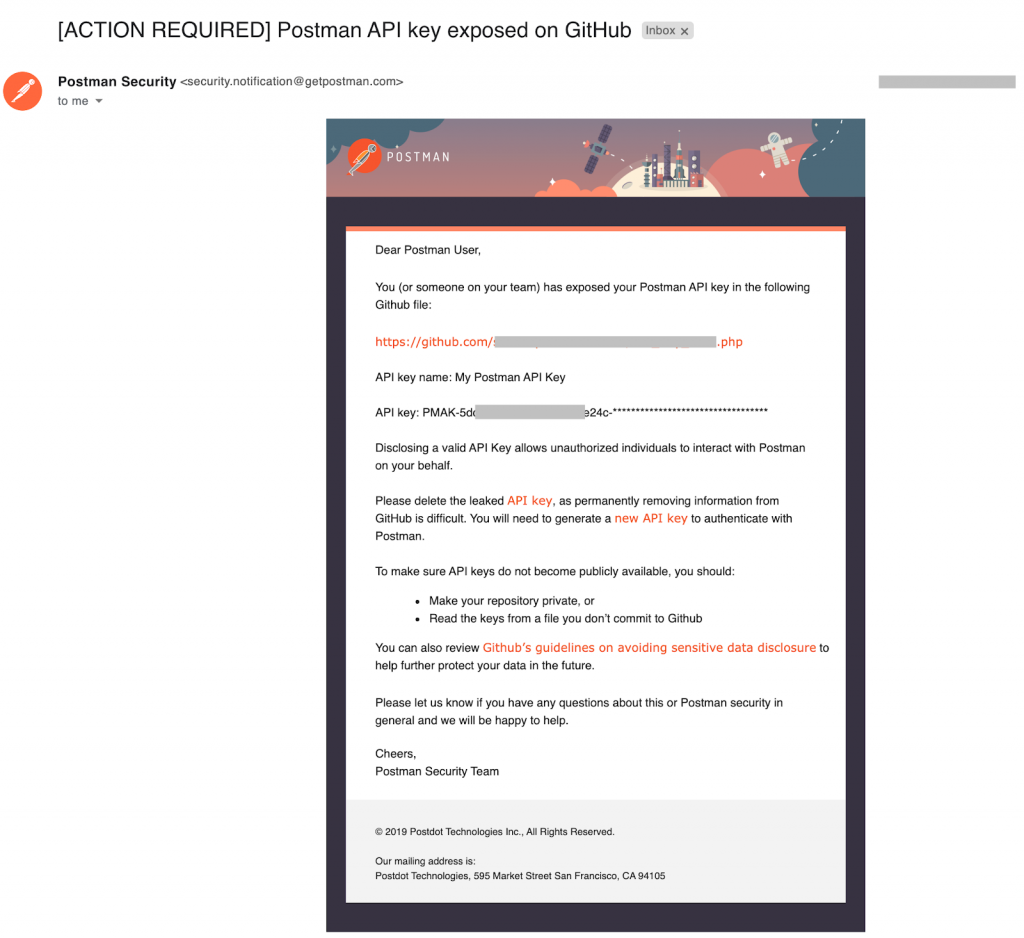
Here’s how it works: GitHub will now scan your code commits for Postman API keys. If a valid key is found, Postman will send you an email alerting you to the situation (see sample email below). If you receive one of these notifications, we advise that you immediately delete any exposed Postman API keys, because as soon as a key is pushed to a GitHub repo it is considered compromised and could leave your data vulnerable. To continue using Postman API, you should then generate a new key from your account and update your client applications to use the new key instead.
The token-scanning service is now active by default and will automatically check any code you commit to GitHub. We advise you to verify your email address with Postman to ensure that you receive these important security notifications.
If you have questions or comments about this Postman topic (or any other), we encourage you to head over to the Postman community page or contact Postman support.

What do you think about this topic? Tell us in a comment below.